Best way to protect your company’s information services? Have a plan in place first
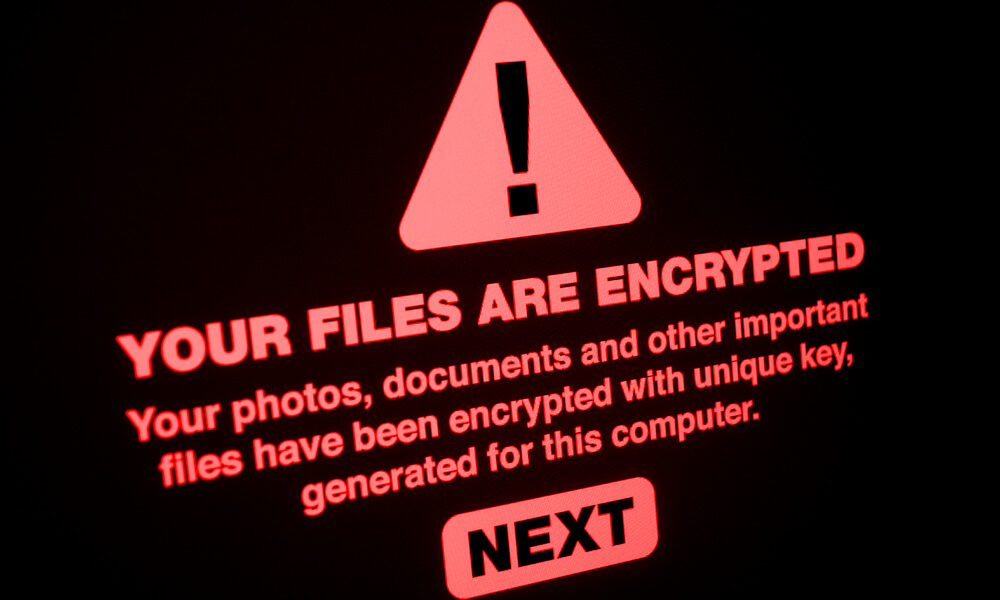
Quincy Mayor Mike Troup on May 24 said the city has spent about $150,000 on outside consultants and $500,000 for an encryption key to regain access to the city’s information services systems.
The City Council approved May 23 an emergency payment for cyber security consulting, emergency purchases and retaining the firms of Mullen Coughlin, LLC, of Devon, Pa., and Kroll Associates, Inc. of New York for information security services and cyber cryptocurrency and ransomware negotiation services.
The Federal Bureau of Investigation and the Department of Homeland Security recommend entities do not pay ransoms. The Gartner Group, one of the world’s leading information technology research firms based in Stamford, Conn., lists several reasons to not pay.
- Encrypted files are not always recoverable.
- Only 65 percent of data is recovered on average, and only 8 percent of organizations recover all data.
- Recovering data can take several weeks.
- There is no guarantee the hackers will delete what they stole.
Many organizations, however, are in a position where they have no choice. No matter the protection used, information being stolen always is a chance.
Jen Miller-Osborn is deputy director of threat intelligence at Palo Alto Networks, an American multinational cybersecurity company based in Santa Clara, Calif. She said, “Nothing’s ever going to be 100 percent (secure). You know, there’s always going to be that chance of something that just wasn’t seen or a zero day (attack) in particular.”
What is an organization to do?
“The key initial first step is (for a company to) actually have to a plan in place to respond to incidents,” Miller-Osborn recommends. “Protections are a key component as well as having federated ones in place.”
Federated? Miller-Osborne says ideally all disparate systems communicate to each other, recognize when abnormal behavior occurs and provide some sort of alerting.
“When you look at how quickly some of these intrusions spread, especially ransomware, you can’t rely on one person to see that alert and isolate that machine fast enough,” she said. “It has to be done at machine speed, where that behavior is seen, that attempt to spread to other computers. That automatically triggers defenses that pull those systems offline.”
Why not use your system backup and restore?
“I’ve been unfortunately involved in a number of incidents where the backups were either also encrypted, because they were available from the primary network, or they had some sort of other data quality issues where they were actually unable to use them to restore,” Miller-Osborne said.
Rather than pay the ransom, build a new e-mail server. Right?
Not so fast, according to Binto George, professor of computer science and network technology at Western Illinois University.
“That’s actually an interesting question. The problem, again, is the data,” George said. “A server is only as good as the data it stores. If the data is encrypted, you are stuck.”
Troup said at the May 9 City Council meeting the attack apparently started at the Quincy Public Library before spreading through other departments. It’s not surprising the attack came through the library, which by its nature is open to anyone to use.
“People might have to resort to online research for things, download things (that unintentionally contain Malware) or someone uses a USB drive. Those are all vectors for ransomware,” George explained.
Municipalities can be easy targets.
“To be quite honest, because the attackers know they don’t have the resourcing and the money invested like larger organizations, they know they’re more likely to have an easier time compromising them,” Miller-Osborn said. “While they might not make as much money off of a municipality, you can do them at volume. They can add up.”
George said funding issues are a problem most of the chief information security officers face, because if something like this doesn’t happen, it is very hard to come up with a business case to request funding.
“The reason for that is that this leadership focuses on business and day-to-day activities,” George said. “Especially if you have a very safe town, you always feel like you tend to trust people more. You would sort of assume that OK, we’ll be fine.”Situations like these put the IT Department in a tough spot, according to George.
“Here is the problem,” George said. “As an administrator, you need to be 100 percent right all the time. If I’m an attacker, they don’t have to follow the law. All they want is to be right just once.”
Miller-Osborn suggests that at some point, a business decision must be made on investment versus risk and where you’re going to be comfortable.
“Unfortunately, especially as we’re moving forward, and more and more things are interconnected, that’s just going to continue to become a bigger and bigger deal,” she said. “In districts where they aren’t able to secure things, the attackers are recognizing they are easy ways to potentially get money, because they don’t have those protections in place.
“The only thing that’s going to make them safe is spending on the protection side.”
George says situations similar to the one that happened in Quincy are not really anybody’s fault, other than the people trying to do this.
“The world is not perfect, and there are groups of people who are always there to attack,” George said. “Therefore, it is wise to spend money and budget money for cybersecurity.”
Miss Clipping Out Stories to Save for Later?
Click the Purchase Story button below to order a print of this story. We will print it for you on matte photo paper to keep forever.

